SQL Injection is a technique that exploits the security vulnerability of a website. It usually happens if a user enters either incorrect filter for string characters embedded in SQL statements or input is unexpectedly executed. These errors can harm your website in the long run. At Candidinfo, we employ the latest in cutting edge technologies and makes your e-business error-free. Everything from giving your site a customized open source solution to an updated look and feel, we make the process simple and effective.
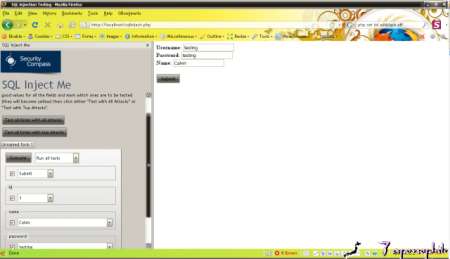
Security Compass has introduced a firefox add-on “SQL Inject Me.” It will submit your form and replace the values in the existing form field with strings that are considered as possible attack. This tool will send all the possible database escape string as well as search for any error messages returned. Finally, it will render as HTML format in page.
Once you have installed the addon, go to Tools-> SQL Inject Me-> Open SQL Inject Me Sidebar. You will find a sample form that will proceed an update action into database while form is being posted. To make sure the form is tested, fill in the fields with good values and mark the checkbox.
Here a sample of the tool, after you test the form for all attacks:
Here’s is the final output. The result marked with red color background are error messages, which have been returned by
database.
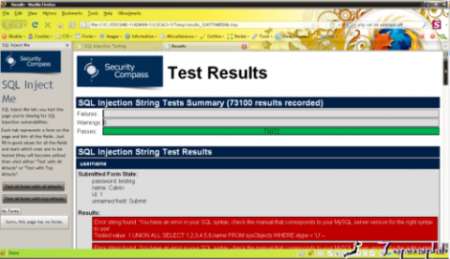
Although, this tool looks for all the possible input that may harm your system but it doesn’t provide protection for password hacking, firewall attacks, etc. However, SQL Injection Me is still quite useful and helpful tool for you, as it tests SQL Injection vulnerabilities.Download SQL Injection Me now – to make testing an easy process.
To know more about testing and other web development services, click here.